DETECTION-FIRST COUNTER-UAS SYSTEMS
Advanced Counter-UAS Equipment & Tailored Security Solutions
A specialized counter-UAS systems provider focused on detection-driven and electronic countermeasure solutions
Passive RF Detection
Early warning for dense and complex airspace.
Adaptive Countermeasures
Tracking, jamming, and navigation deception in one workflow.
Field-Proven Deployment
Built for defense, public security, and critical infrastructure.
Focused on Counter-UAS Excellence
Detection First
Early warning through passive RF sensing and multi-source detection, enabling timely and reliable drone threat awareness.
Layered Defense
From identification and tracking to jamming and navigation deception, we deliver adaptive countermeasures across complex environments.
Mission-Driven Solutions
Purpose-built systems designed for defense, law enforcement, and critical infrastructure protection — reliable, scalable, and field-proven.



Core Capabilities
What we deliver across the counter-UAS lifecycle

Multi-Modal Detection & Counter-UAS Application Scenarios
Multiple sensing modalities integrated to support diverse counter-UAS application scenarios.
RF Detection
Passive & long-range RF sensing
Direction Finding & Localization
AOA / TDOA precision tracking
Signal Classification & Identification
Signal / Protocol & Drone Type Identification
Whitelist & Blacklist Management
Identity-based access control

Long-duration identification and tracking of unauthorized intruding drones.
Focusing on continuous target tracking and precise localization, transforming early detection into actionable situational awareness.
Direction Finding
RF-based direction finding and tracking
Signal-Based Localization
Direction-based localization of aerial targets
Tracking
Continuous tracking during active operations
Deployment
Portable and fixed deployment options

Identification & Analysis
Signal-based identification and behavioral analysis for reliable drone threat assessment.
Drone Type Identification
Drone type identification based on RF signals
Protocol & Signal Analysis
Protocol and communication signal analysis
Electronic Fingerprint Recognition
Electronic fingerprint recognition for target differentiation
Threat Level Assessment
Threat level assessment based on behavior patterns

Integrated Counter-UAS Countermeasures
Coordinated jamming, navigation deception, and denial measures, dynamically triggered by real-time threat assessment.
Intelligent Jamming Control
Targeted RF interference with minimal spillover
GNSS Spoofing & Navigation Deception
Controlled navigation manipulation for safe mitigation
Layered Response Strategy
Graduated response aligned with threat level
System-Level Integration & Control
Unified command across detection and response
Counter-UAS Solutions
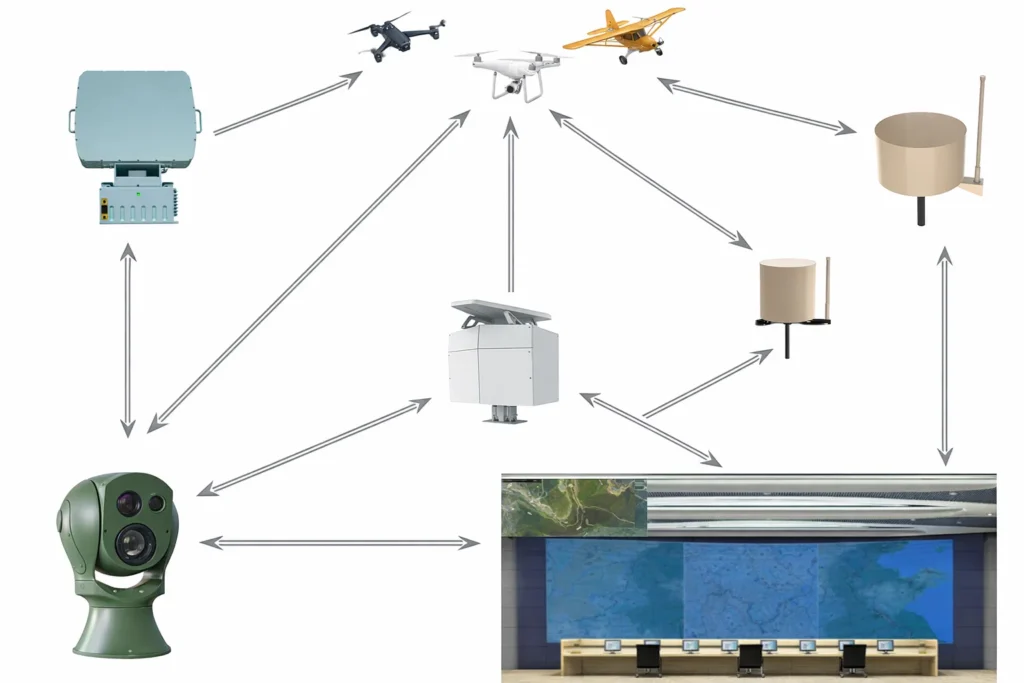
Integrated Counter-UAS Solution
Deployable as standalone units or integrated into centralized command systems

Mobile Counter-UAS Operational Solution
Scalable from single-site protection to regional defense networks
Explore Our Products
Navigate detection, defense, and deception platforms by mission profile.
Deployment Highlights from Real Scenarios
Deployment references across portable, fixed, and government-led operational contexts.

Portable Units in Action
Field-tested across complex operational environments

Central Command Systems
Used by public security and critical infrastructure operators

Government Collaboration
Deployed in multiple government-led security projects



